什么是 WAF?| Web 应用防火墙解读
WAF 在 Web 应用与互联网之间创建防火墙;此类防火墙有助于缓解很多常见攻击。
学习目标
阅读本文后,您将能够:
- 定义 Web 应用防火墙
- 解释黑名单与白名单 waf 之间的区别
- 了解基于网络、基于主机和基于云的 waf 的优缺点
相关内容
想要继续学习吗?
订阅 TheNET,这是 Cloudflare 每月对互联网上最流行见解的总结!
复制文章链接
什么是 Web 应用防火墙 (WAF)?
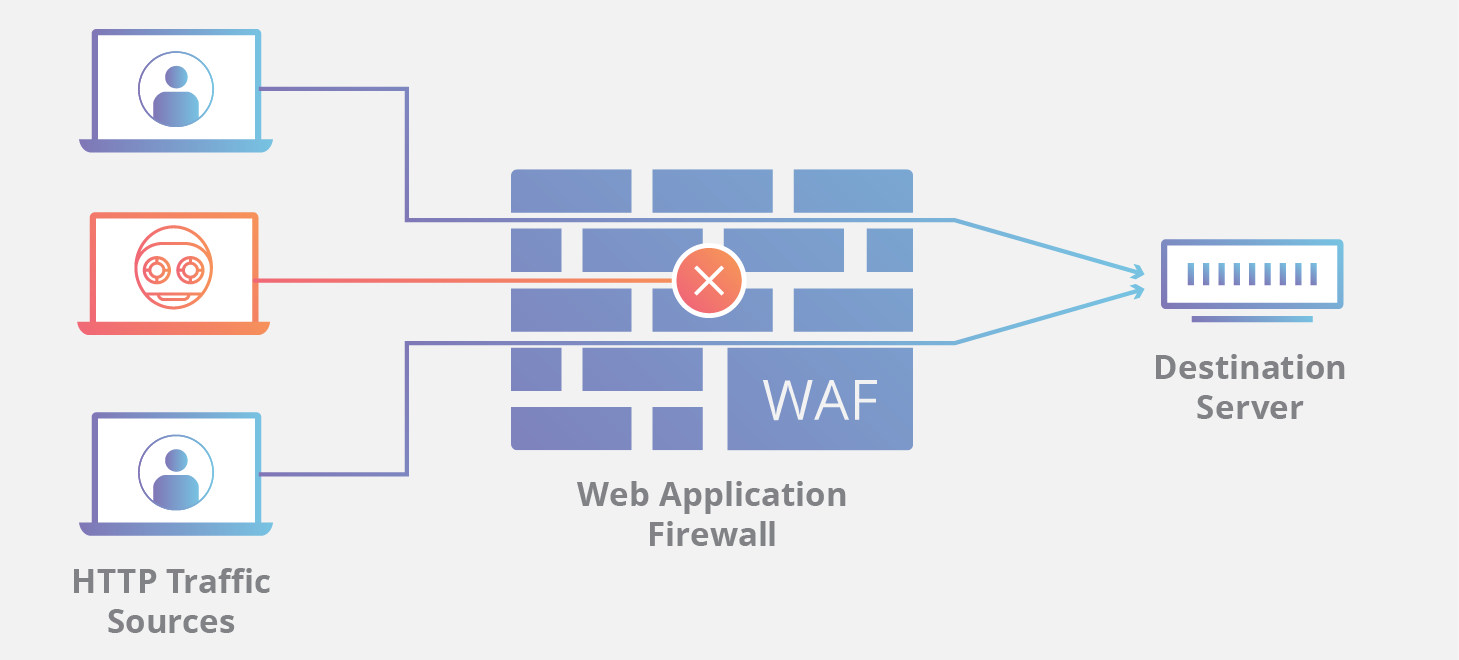
Web 应用防火墙 (WAF) 会过滤和监测 Web 应用与互联网之间的 HTTP 流量,以此来保护 Web 应用安全。它通常会保护 Web 应用免受各种形式的攻击,例如cross-site forgery、Cross-Site Scripting (XSS)、文件包含以及 SQL 注入等。
WAF 属于协议第 7 层防御策略(OSI 模型中),并不能抵御所有类型的攻击。此攻击缓解方法通常隶属于一套工具,整套工具共同针对一系列攻击手段建立整体防御措施。
通过在 Web 应用前端部署 WAF,可在 Web 应用与互联网之间形成一道屏障。虽然代理服务器通过中介保护客户机的身份,但 WAF 是一种反向代理,引导客户端通过 WAF 到达服务器,从而防止暴露服务器。
WAF 通过一组通常称为“策略”的规则进行运作。这些策略旨在过滤恶意流量,防止受到应用漏洞的侵害。WAF 的部分价值在于可以快速简便地修改策略,因而可以更迅速地响应不同的攻击手段。在 DDoS 攻击期间,可通过修改 WAF 策略快速实施速率限制。
黑名单与白名单 WAF 之间有什么区别?
基于黑名单(消极安全模型)运行的 WAF 可防范已知攻击。您可以将黑名单 WAF 想象为俱乐部保镖按指示拒绝接待不符合着装要求的客人。相反,基于白名单(积极安全模型)的 WAF 仅允许接受预先批准的流量。类似于奢华派对保镖,只接待出席名单列出的客人。无论黑名单还是白名单,二者都有各自的优缺点,因此很多 WAF 提供混合安全模型,综合实施两种方法。
什么是基于网络、基于主机和基于云的 WAF?
WAF 可以通过三种不同的方式来实施,每种方式都有各自的优缺点:
- 基于网络的 WAF 通常基于硬件。由于采用本地安装模式,因而可以最大限度地缩短延迟,但基于网络的 WAF 费用最昂贵,而且还要安装和维护物理设备。
- 基于主机的 WAF 可完全集成至应用软件。这种解决方案的成本低于基于网络的 WAF,而且还能提供更多定制功能。基于主机的 WAF 的缺点在于,占用本地服务器资源,实施起来复杂,而且还会产生维护成本。这些组件通常需要预留维护时间,可能成本较高。
- 基于云的 WAF 是一种极易实施的经济型方案;通常提供一站式安装服务,就像更改 DNS 来重定向流量一样简单。另外,基于云的 WAF 的前期成本最低,因为用户按月或按年支付安全即服务费用。基于云的 WAF 还可以提供持续更新解决方案以抵御最新威胁,用户无需额外开展工作或投入成本。基于云的 WAF 的缺点在于,用户将责任转嫁给第三方,因此对他们而言,WAF 的某些功能可能成为黑盒。(基于云的 WAF 是一种云防火墙类型;了解有关云防火墙的更多信息。)
了解全球连通云如何让公司使用基于云的 WAF 解决方案来保护其网站安全。
FAQs
What is a web application firewall (WAF)?
A WAF helps protect web applications by filtering and monitoring HTTP traffic between an application and the Internet. It defends the application layer, protecting servers from common threats like SQL injection, cross-site scripting (XSS), and cross-site forgery.
How does a WAF protect web applications?
By deploying a WAF, a shield is placed between the application and the Internet. Unlike a standard proxy that protects a client, a WAF is a reverse-proxy that protects the server by requiring all clients to pass through it before reaching the application.
What are the differences between blocklist and allowlist WAF models?
A blocklist (negative security model) denies traffic based on known attack patterns. In contrast, an allowlist (positive security model) only admits pre-approved traffic. Many WAFs use a hybrid of these models.
How can WAF policies be used during an active attack?
WAFs operate through sets of rules called policies that filter out malicious traffic. Because these policies can be modified quickly and easily, they allow for a fast response to new attack vectors, such as implementing rate limiting during a DDoS attack or blocking a new vulnerability exploit.
What are the three primary ways to implement a WAF?
WAFs can be implemented in the following ways: Network-based WAF: Typically hardware-based and installed locally to minimize latency. Host-based WAF: Integrated into the application software, offering more customization but consuming local server resources. Cloud-based WAF: An affordable and easy-to-implement security as a service option that provides consistent updates against new threats with minimal upfront cost.
Why might a company choose a cloud-based WAF over other options?
Cloud-based WAFs are often preferred because they offer turnkey installation and require no additional work or cost for protection against the latest threats. This process can often be as simple as a DNS change. While cloud-based WAF customers hand over some responsibility to a third party, they benefit from a solution that is updated to block new attacks without any effort on their end.